1. The Anatomy of a Phishing Email
Phishing emails are digital wolves in sheep’s clothing. At first glance, they appear innocuous, often impersonating trusted entities such as banks, businesses, or government institutions. Their primary goal? To trick recipients into revealing sensitive data like passwords, financial details, or personal identifiers.
These emails capitalize on subtle psychological tricks, exploiting trust and urgency. Phishers rely on the average user’s instinct to act quickly rather than inspect. Understanding the anatomy of these deceptive messages is the first step to avoiding the bait.
2. Suspicious Sender Information
Scrutinizing Email Addresses
While phishing emails often mimic legitimate companies, the sender’s address reveals critical clues. Instead of an authentic domain (e.g., @paypal.com), you may encounter misspellings like paypalsupport@gmail.com or unfamiliar variations like @secure-accounts.net. Always hover over the “From” address to see its true origin.
The Trick of Impersonation
Advanced phishing attacks may employ spoofing, where a sender appears to be someone you trust—like your boss or a customer service agent. The sophistication lies in subtle typos or the use of public-facing contact names. If something feels “off,” don’t take it at face value. Contact the individual or company directly through trusted means to confirm authenticity.
3. Unusual or Urgent Language
The Role of Emotional Manipulation
Phishers exploit human psychology to provoke emotions. Words like “urgent,” “immediate action,” or “account suspension” trigger panic, prompting users to bypass their usual caution. By creating fear or excitement, scammers push recipients into impulsive decisions.
Common Phrases That Raise Red Flags
Be wary of emails containing phrases such as:
- “Verify your account now!”
- “Your payment failed—click to fix it!”
- “You have won a prize!”
These messages often have exclamation points, capitalized words, or aggressive calls to action. The urgency is deliberate; its purpose is to override rational skepticism.
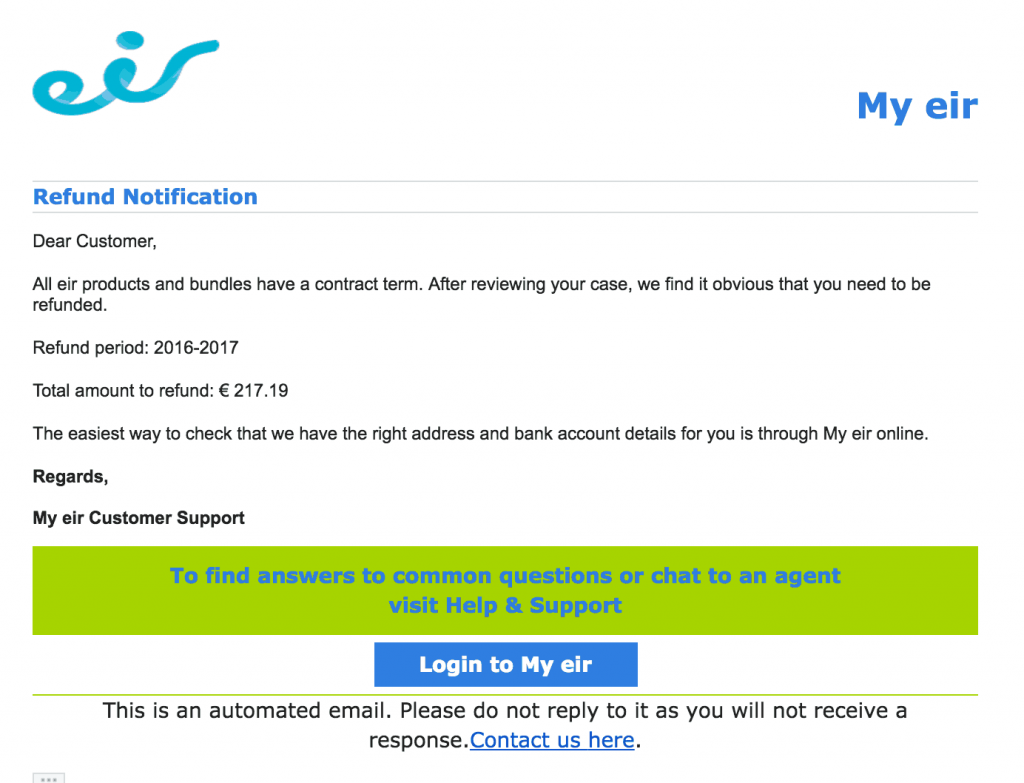
4. Inconsistent or Poor Design
Formatting Issues and Branding Inconsistencies
Legitimate companies invest in clean, professional communication. Phishing emails, however, frequently contain visible errors. Watch for odd font changes, misspellings, or uneven logos. If the formatting feels disjointed or unpolished, treat it as a red flag.
Spotting Unusual Attachments or Links
Phishing often hides malware or credential-harvesting tools in attachments or links. Never click on a link without inspecting it first. Hovering over links reveals their destination URLs, which can expose misleading or unfamiliar domains. Legitimate companies rarely send attachments without prior notice. If an unexpected file appears—especially .exe, .zip, or macro-enabled formats—it’s best left unopened.
5. Analyzing the Call to Action
Pressure Tactics: Time-Sensitive Requests
Phishers excel at creating artificial urgency. Phrases like “Your account will be locked in 24 hours” are meant to provoke anxiety. These time-sensitive traps cloud judgment, compelling you to act without verifying.
Demands for Personal Information
Legitimate businesses rarely, if ever, request sensitive details—like passwords or Social Security numbers—via email. Be especially wary of requests that redirect you to “login portals.” Fake landing pages may look authentic but are designed to capture your credentials. A legitimate company would encourage secure, verifiable interactions through official channels.
Final Thoughts
Phishing emails are constantly evolving, becoming more sophisticated and harder to identify. Awareness is your greatest shield. By carefully inspecting sender details, language, formatting, and calls to action, you can defend yourself against falling prey to these deceptive tactics. When in doubt, err on the side of skepticism and verify through trusted means—because online vigilance is no longer optional; it’s essential.

 Did you know that over 13% of Irish internet users have experienced fraud of some description, while 16% of them had reported having their social media or email accounts hacked? The Irish Times surveyed over 1,000 Irish men and women and found that anti-virus use in Ireland is well below the EU’s 61%.
Did you know that over 13% of Irish internet users have experienced fraud of some description, while 16% of them had reported having their social media or email accounts hacked? The Irish Times surveyed over 1,000 Irish men and women and found that anti-virus use in Ireland is well below the EU’s 61%. A recent warning issued by An Garda Síochána about a callback scam targeting Irish users of WhatsApp should serve as a reminder to company owners that their business networks, including their mobile messaging platforms, face a variety of risks.
A recent warning issued by An Garda Síochána about a callback scam targeting Irish users of WhatsApp should serve as a reminder to company owners that their business networks, including their mobile messaging platforms, face a variety of risks. The 2018 update of the Oxford English Dictionary will include ransomware as a new entry, and this announcement just happens to coincide with a new zero-day exploit that bypasses security measures of popular cloud computing services such as Office 365 and Google Drive.
The 2018 update of the Oxford English Dictionary will include ransomware as a new entry, and this announcement just happens to coincide with a new zero-day exploit that bypasses security measures of popular cloud computing services such as Office 365 and Google Drive.